The CIS Critical Security Controls for Effective Cyber Defense Center for Internet Security Computer security Information security, others, text, logo, information Technology png | PNGWing

The CIS Critical Security Controls for Effective Cyber Defense Computer security Center for Internet Security SANS Institute, Cyber Essentials, text, information Technology, technical Standard png | PNGWing

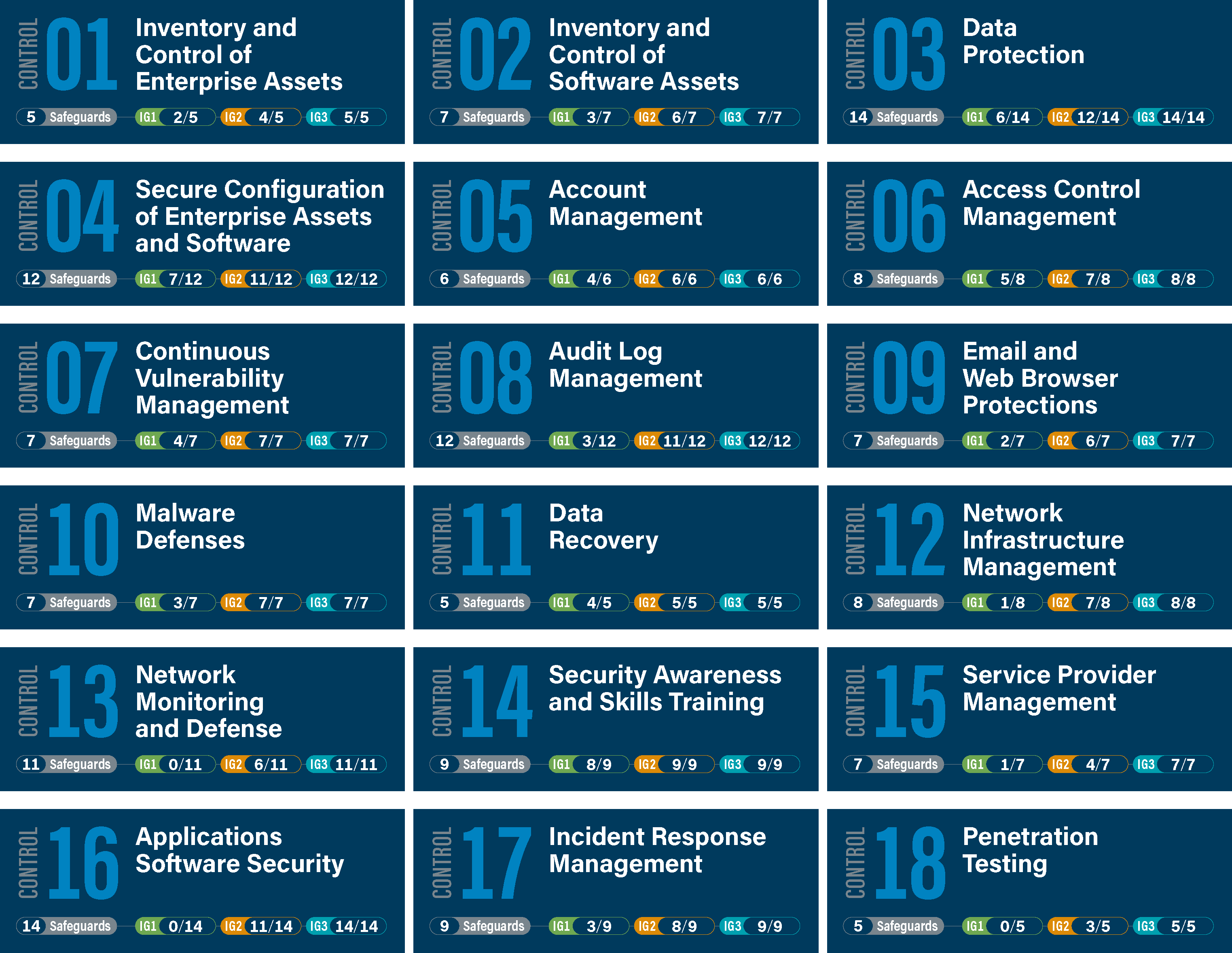
Cyber Security Best Practices: No. 1: Hardware Inventory | ITPro Today: IT News, How-Tos, Trends, Case Studies, Career Tips, More
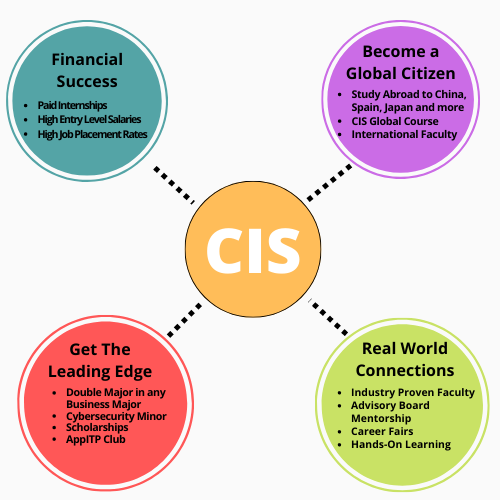
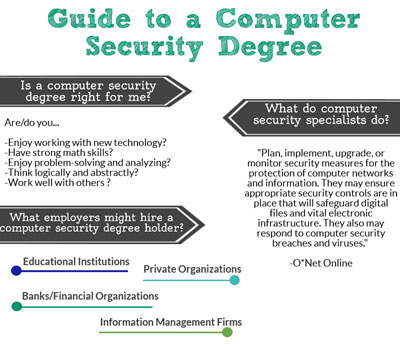
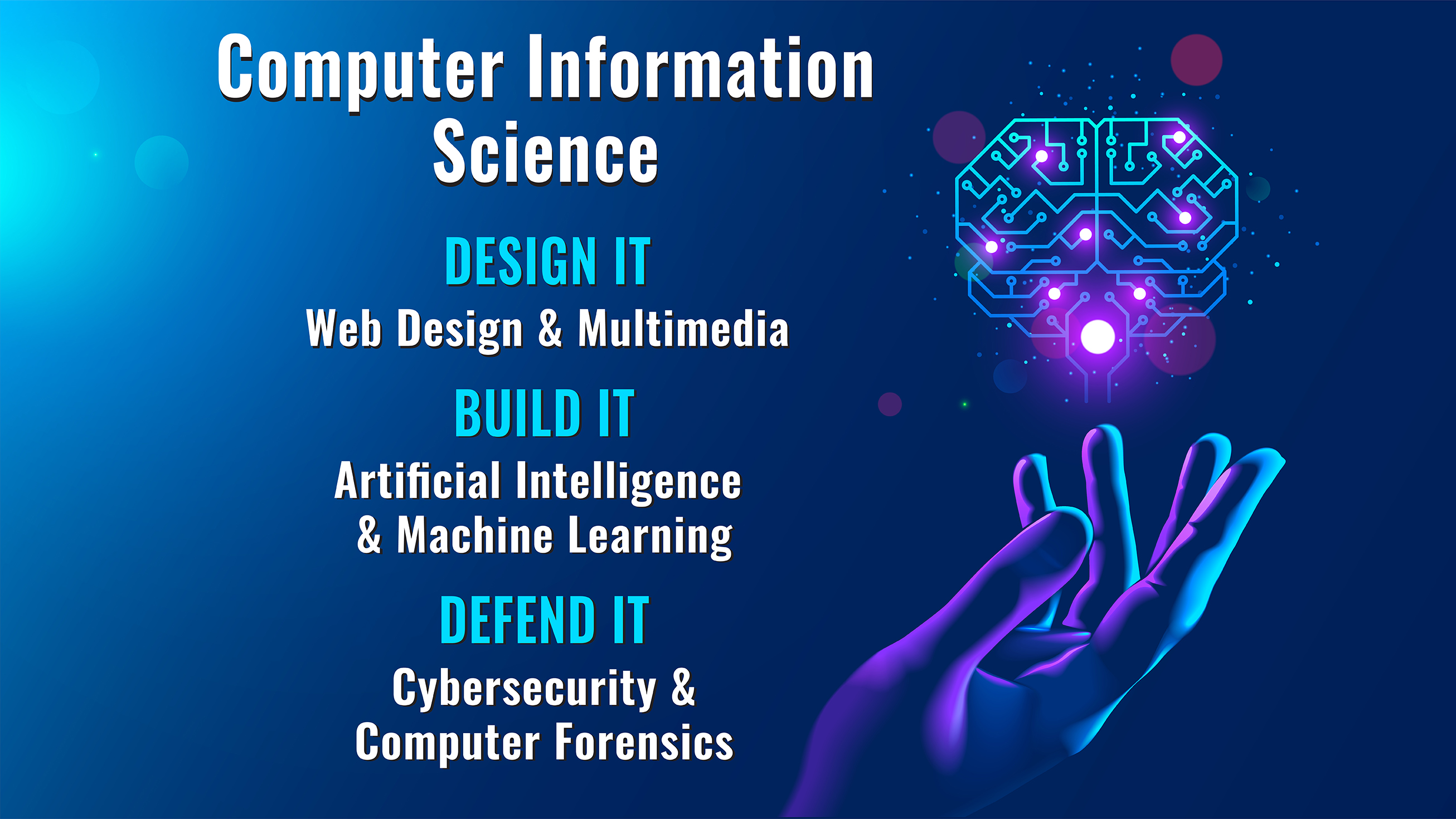
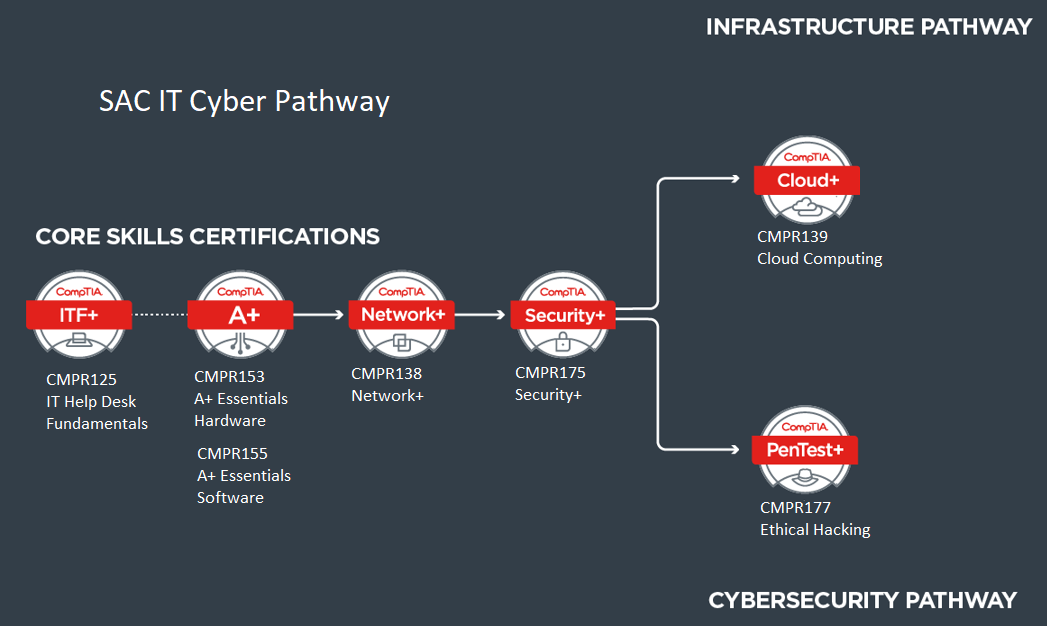
Program: Computer Information Systems (AAS), Cyber Security Concentration - Central New Mexico Community College - Acalog ACMS™

Computer Information Systems (CIS) vs. MIS, Computer Science, IT, Cybersecurity, and Data Science - YouTube



:max_bytes(150000):strip_icc()/computer-and-information-systems-manager-525998_final_HL-f6355457b1494f4f84b26ef9ac2158c2.png)










/prod01/cdn-pxl-elginedu-prod/media/elginedu/academics/departments/digital-technologies.jpg)